- Summary
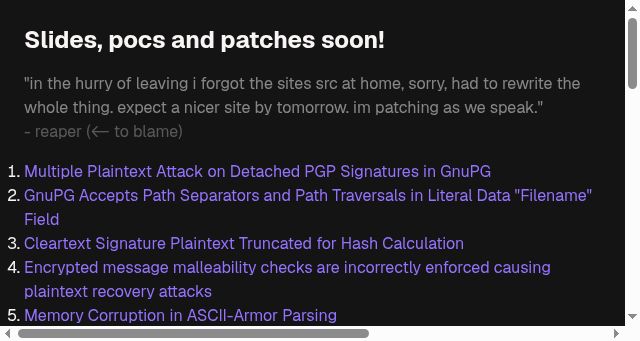
- Several critical vulnerabilities in the GnuPG authentication framework allow attackers to bypass security controls effectively. Specifically, a malicious path can be injected into the file name field to retrieve the plaintext underlying a detached Private Key Generation (PGP) signature. This information enables attackers to perform targeted brute-force attacks, effectively replacing the encrypted message with a readable copy. Additionally, corrupted messages containing path separators can trigger memory corruption in ASCII-armored parsers, further compromising integrity checks. Furthermore, attackers can manipulate the trusted comment injection (minisign) protocol to add arbitrary subkeys to the public key, giving them unrestricted access to private data.
The implementation of cleartext signature frameworks is also highly susceptible to format confusion attacks, where the underlying plaintext is swapped out. This allows attackers to forge valid signature headers, leading to forged messages. Such forgery can enable offline key recovery attacks where a stolen key is used to decrypt a message, and it can enable polyglot attacks that allow a malicious sender to send messages in multiple formats simultaneously. These weaknesses have led to instances where output fails to correctly distinguish between successful verification and malicious content within message bodies. In addition, legacy digest algorithms like SHA1 may be used during critical signature verification checks, making the system more vulnerable to cryptanalytic threats. - Title
- gpg.fail
- Description
- gpg.fail
- Keywords
- signature, path, message, attacks, comment, injection, forgery, slides, patches, hurry, leaving, sites, home, rewrite, whole, thing, site
- NS Lookup
- A 104.21.9.53, A 172.67.159.29
- Dates
-
Created 2026-03-10Updated 2026-04-07Summarized 2026-04-06
Query time: 739 ms